|
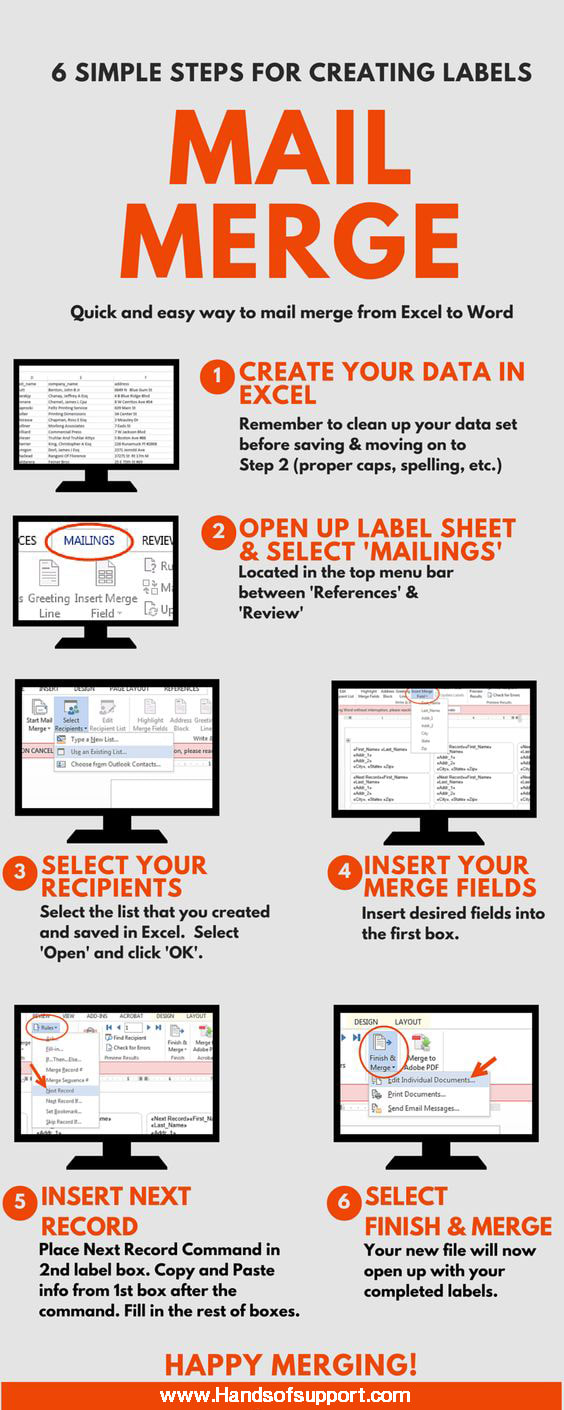
The advantages of mail merge is that the feature saves you time and efforts. Producing mass mailings is much simplified, especially compared to the process of preparing individual letters or envelopes to many people. If you follow these simple steps it can save you even more time.
0 Comments
Free Software – Pictures and Graphics Programs
1. Paint.net Adobe Photoshop is, of course, the standard when it comes to graphics editing. But, it comes with a hefty price tag. After some research I found a highly recommended alternative called Paint.net. Paint.net offers functions similar to photoshop, without any cost! Between paint.net and PicMonkey (below) I have been able to edit and create all the graphics for this blog and for my personal use. 2. PicMonkey Paint.net is a great tool to edit graphics. But, to create a graphic, I use an online program called PicMonkey. PicMonkey is a great choice for editing pictures, adding text and fun graphics, borders, etc. It’s very user friendly, quick and easy to use. The majority of the graphics on this blog were created with PicMonkey and Paint.net. 3. FastStone Image Viewer FastStone Image Viewer is an easy to use program which makes organizing and viewing digital pictures a breeze. It also includes some photo editing features and allows you to create slideshows. I am an extremely organized (maybe borderline OCD) person so I had to come up with a way to organize my digital pictures or I’d go over the edge! Free Software – Video Tools 4. Open Broadcaster Software Open Broadcaster Software is screen capture software which can be used for live streaming and recording. We use this program to create computer tutorials for our YouTube page. 5. Real Downloader RealDownloader is a free program which allows you to download videos you find on the internet. In this post I go into depth on how I use RealDownloader to download YouTube videos to save them on my computer for later use. 6. VLC Media Player My expertise in video files and formats is definitely lacking but, I do know that I’ve been frustrated a time or two because my standard player can’t read the file format and won’t play the video. VLC Media Player solves all that. This player is awesome as it can read almost any file format you come across. It can play from files, CD’s, DVD’s and live streaming. In addition, it gives you the capability to convert files to a different format if you wish. Free Software – File and Data Programs 7. Dropbox In this post we review what the cloud is and compare various cloud services programs. Dropbox has been my go to cloud storage option at work and at home for years now. It’s easy to use and the content is accessible on all my devices. In addition, their folder sharing makes it easy to share content with others. 8. Evernote Evernote is a popular program which helps you organize your life. It’s great for jotting down notes, organizing thoughts, keeping notebooks of recipes, whatever! The uses for this handy little software seem endless. I like it because I can capture thoughts and notes, keep them organized and access them from any computer or device quickly. If you’re interested in learning more about Evernote or finding uses for it check out this post. Free Sofware – Computer Tools 9. Classic Shell Well, in this post we walk you through getting that classic start menu back using classic shell. I highly recommend anyone using windows 8 or 8.1 who enjoyed their old look installs this program. 10. TeamViewer While most of us are comfortable with the idea of sharing our files in the cloud so you can access them anywhere not as many are probably aware of how easy it is to work on your own computer remotely. Teamviewer is a powerful free tool which allows you to connect to your computer from anywhere you have an internet connection. (LogMeIn is also a great service if you don’t mind a paid option.) 11. Folder Size Explorer With programs getting larger and all of us taking more digital pictures filling up your hard drive is becoming a problem we’re all more aware of. However, what’s taking up all of the room on your hard drive? It’s hard to figure out since windows explorer no longer shows you the sizes of your folders. In this post we walk you through how to use Folder Size Explorer to find out what’s taking up all your hard drive space and figuring out what to delete. 12. Mozilla Firefox When Internet Explorer started having technical glitches and security problems I did some research on alternate internet browsers. While Google Chrome is a popular choice I am conscious of all the information google collects about me and didn’t want to provide them that much more (a hopeless cause maybe). Then I came across Mozilla Firefox. The browser is clean, easy to use and I’ve converted to using it at home and work for a few years now with no complaints. Free Software – Security Tools 13. Avast Everyone needs to have an antivirus software. Avast is a free antivirus software that’s just as effective as some of the paid options. 14. Avira Avira is another free antivirus software with excellent reviews. While you shouldn’t install both Avast and Avira on your computer at the same time, either of these options is an excellent choice to help you keep your computer and information safe. Note: I’ve recently heard good things from some IT folks about Eset anti-virus software. 15. Malwarebytes Malware is similar to viruses but attacks a computer slightly differently. Therefore, you should always have malware protection on your computer. Malwarebytes is one of the most highly recommended malware protection programs available. I’ve used it to successfully clean up infected computer and trust it immensely. Which free software and tools do you use the most? Please share with us below in the comments. We love discovering new resources! You’re smart.
You don’t use passwords like the perennial 123456 and qwerty. Or even slightly better ones, like Cassie86 or Cubs1908. Because you put some thought into them, your passwords are better than those, right? Maybe. But unless you avoid a little-known mistake recently uncovered by password researchers, there’s a good chance your passwords will still be far easier for hackers to crack than you think. Can you tell how strong a password is? To see, try to figure out which of these four are a pushover for hackers. Zdhkqjbu83 74Xmbgdapw Bmukwes3901! lw;62v74y Spoiler: They’re all an easy mark for hackers, even though every one is 9 or more characters long and contains a mix of both letters and non-letters. How can such apparently strong passwords be so weak? The short answer is that they follow some of the most common patterns of composition that people use to create passwords, patterns that weaken them. Beat the clock How does a hacker get hold of your password? Most likely, through a breach of a customer database like the one that recently let criminals obtain confidential celebrity photos from Apple’s iCloud. (According to Apple, the iCloud database itself was not breached). Since many passwords are stored in such a way that they can’t be directly read by people, hackers often use software to crack them. The longer it takes to crack a password, the less likely the hacker will succeed. If it takes too long, the hacker may give up and move on to easier prey. Long passwords comprised of a variety of letters, numbers, and special characters can better withstand cracking software than can short, simpler ones. However, when something about a password’s composition is too predictable — it begins with an upper case letter, for example, or includes a recognizable word — it can be cracked much more quickly. Games users play Just how predictable are people in composing passwords? Even when they’re following an organization’s password guidelines regarding length and mix, it turns out, most compose passwords in very similar ways. In a 2013 study for DARPA (the Federal Defense Advanced Research Projects Agency) called Pathwell, security consulting company KoreLogic found that, among the thousands of users within an unnamed Fortune 100 company, roughly half had relied on just five patterns to compose their passwords and 85 percent had relied on just 100 patterns. (KoreLogic found similar predictability within a variety of other companies). Here are the three most common patterns KoreLogic found among the thousands it identified in those companies: • One upper case, then 5 lower case, then 2 digits (Example: Dulith57) • One upper case, then 6 lower case, then 2 digits (Example: Abugmar64) • One upper case, then 3 lower case, then 4 digits (Example: Itio1981) Which of these mistakes do you make? It’s not practical to try to avoid every one of the many patterns KoreLogic found. But you can still create better passwords by steering clear of some of the most common mistakes people make: • Starting with an upper case letter followed by lower case letters • When a password isn’t long enough, adding a letter or two to the base word • Putting digits, especially two or four of them, before or after the letters • When a special character is required, using “!” and putting it at the end • Not using two special characters in the same password Don’t rely on password checkers When creating a password, you may be tempted to use online password checkers to test the strength of those you’re considering. Beware: When I tried four of the most popular checkers, How Secure is my Password, Password Meter, Microsoft’s Password Checker, and Kasperky’s Secure Password Check, only Kaspersky’s clearly informed me that the apparently strong password I submitted was actually far weaker than it appeared. Even Gmail’s own password strength tester labeled that password as “strong.” How to make passwords less predictable I won’t suggest any compositional patterns here because, once published, they would immediately become a target for hackers. Instead, here are a few rules of thumb to keep your passwords from becoming too predictable: • Avoid beginning the password with an upper case letter — or maybe even any letter • Create an acronym using the first letter of each word in a memorable sentence, as suggested by security expert Bruce Schneier — example: t2cmlp,@yh (“Try to crack my latest password, all you hackers”) • Resist your natural tendency to mimic familiar words and phrases • Use multiple special characters in the same password • Don’t always place digits adjacent to each other |
Archives
August 2018
Categories |




 RSS Feed
RSS Feed

